Digital Property

Digital Property or digital assets is data that is owned by either an individual or business. Information stored on personal hard drives, ranging from, but not limited to, text documents, emails, code files, photos, and video are considered digital property [2]. Additionally, information collected from the Internet that can be converted into binary form, is also considered digital property.
Contents
An Expanding Empire of Digital Property
The notion of digital property first appeared in a paper by Albert van Niekerk in 2007 proposing management strategies of media assets (MAM). Niekerk characterized digital assets as having the traits of binary form and classified rights to ownership. Two of the three forms of digital assets, images and multimedia, Niekerk proposed should fall under the definition of a media asset and the other textual content is not discussed in great detail in his paper. [3] In 2013, this definition was further expanded in the paper A New Asset Type: Digital Assets which added the characteristics of reusability and longevity to list of attributes defining a digital asset.[4] As the digital world is expanding at an unprecedented speed as individuals and businesses move towards the trend of greater online presence. In other words, information is being commercialized and distributed in mass and the presence of digital assets holding monetary or sentimental value is becoming more prevalent in society[2]. The improved user convenience and organization characterized by digitalizing information is accelerating this movement. This means that everyone is storing more data digitally, and the global digital property content is multiplying. Humanity is interacting with digital technologies at an exponential rate, leading some to argue that it can be difficult to differentiate between online and offline personas[5]. It is contested that the the once strictly digital cyber space is now an indistinguishable part of humanity's natural modern environment[5]. With this trend of greater online interaction and content capacity comes the necessity for greater cultural and legislative change accordingly.
Legislation Regarding Digital Property
The United States prides itself in supporting creativity and innovation to enact progress. Therefore, protection of intellectual property is treated as a fundamental right and is highlighted in the constitution. In Article 1, Section 8, Clause 8 it states that Congress has the power to “promote the Progress of Science and Useful arts, by securing, for limited Times, to Authors and Investors, the exclusive Right to their respective Writings and Discoveries”. [6] There was no way for the Founding Fathers to have predicted the digital age we have today in the 21st century, therefore digital property is not mentioned specifically in the constitution. However, they did account for intellectual property protection which was later developed into a system of patents, copyright, and trademark rights and laws. Despite these barriers put in place to protect innovators and promote advancements, the complications of the digital property off-shoot from traditional works skews the property protection process further.
California, which has some of the most developed digital privacy and security laws, has certain statutes that apply to digital assets. California law defines digital assets as any form of digital records or files, which apply to email accounts, blogs, social media accounts, financial accounts, etc. Although ownership and accessibility of these files can vary under a provider's terms of service, the individual who holds the asset is the primary owner. This creates legal ambiguity, such as if a legal executor can access a digital file or social media account after the account holder's death. If the account holder does not provide instructions or information on how to access the file, they cannot gain entry to the assets, since California does not grant authority of digital assets to executors. Assets may continue to exist without proper management or ownership. This includes files, which can hold crucial information, or social media platform information, which may create confusion and ambiguity if they continue to exist after a holder's death. Given the massive amount of online information and growth of digital assets, California is considering updating legislation to help the process of transferring digital asset ownership and management.
Currently the European Union is working to coordinate the protection of intellectual property with technology in light of the increasingly digital age we live in. The United States is also attempting to create legal structure to protect intellectual property in regards to data and technology through the National Information Infrastructure.[7] The difference between countries in stages of integrating digital property protection laws within current legislation poses another problem. The laws vary by country, although the internet network expands worldwide. [8] Exchange of certain information may be legal in one country, but can be communicated across borders instantaneously and become considered illegal sharing of digital property.
Types of Digital Property
There are three main types of digital property:
- Personal digital property: Personal digital property is any information that is stored electronically. When referring to electronically, this can mean data that is stored online or on a physical device. Personal digital property also means any online accounts that are personal to the user. A person's personal digital property is legally theirs and even family members cannot access these legally after a loved one passes away. There is a legislative process to follow to access someone else's personal digital property [9].
- Personal digital property with monetary value: Personal digital property with monetary value is property that generates revenue for personal benefit, such as computing hardware, websites, eBooks, accounts that are used to manage money.
- Digital business property: Digital business property refers to digital property owned by a business. This can mean accounts that are under the business’s name, assets of an online store, any client data, or mailing lists[10].
Ethical Dilemmas
Data Creation, Ownership, and Privacy
Companies pay big bucks for consumer data. Digital data that originates at the level of individuals is often collected by companies using technology such as cookies. Companies who collect this data sell it to other companies for purposes such as targeted advertising. An ethical concern, users whose data is being collected and sold, are often unaware, as data collection is often a topic that goes unread in site's fine print.
The Target Case
An anonymous teen from Minneapolis was sent physical targeted ads by mail because of data that Target gathered from her digital footprint[11]. Generated through her own searches on search engines, Target used the cookies to make the assumption that the young woman was pregnant, and sent her targeted ads for discounted baby products. Because of the data collected and analyzed, Target suspected she was pregnant long before her parents did, resulting in the family discovering her pregnancy through the targeted ads being sent to their house.
Increased accessibility
The digital age enables information to be shared more efficiently through file uploads, mass email chains, and sharing of social media posts, all of which make up digital property. This increased fluidity of information in turn leads to greater accessibility. Instead of physical property being passed along manually, the virtual circulation of digital property creates an expansive network expanding the web worldwide. This increased accessibility makes protection of digital property more complex, as the information can be possessed by numerous people at once without concern for the original source. [8] [7]This continuous process of copying material to be shared with the world can lead to the degradation of content quality as well. [7] Original content can be altered intentionally for example with effects on images and videos, or unintentionally with the composition of pixels degrading or content being lost in the transitional process.
Passwords
With increasing quantifiable data online and on computers, passwords and passcodes have grown more prevalent in cyber space. Digital property can be protected through patents, copyright, and trademark laws, but if the individual proprietors don’t take steps to safe-guard their personal digital belongings through passwords, legislation can do little. The privacy breach that the expansive network of internet users poses to personal digital property can be minimized by strong passwords and diversification of these passwords between different accounts. [12] Many online entities are doing their part to assist users in creating newer, stronger passwords in order to protect their customers personal information and avoid any negative publicity on the corporate side. A method known as nudging is commonly used where websites display pop-ups, occasionally when a user logs-in, encouraging the user to update their password.[13] There can be many different reasons to nudge a user, most commonly this is due to the user retaining the same password for a lengthy amount of time, attempted theft or hack, and as a requirement for employees for various companies. [14] In addition to encouraging users to create strong passwords, many platforms nowadays offer two-factor authentication as a means of furthering the your account security to ensure protection of your online property and data.
Violations of patents, copyrights, and trademarks

Current legislation regarding digital property attempts to set boundaries and sanctions as punishment for infringing on intellectual and contractual property. Patents, copyrights, and trademarks are violated constantly, as artists and inventors have difficulty distinguishing inspiration from originality. As Snapper details about plagiarism, authorization to digital property is outlined with very fine lines, and interpretation of patent and copyright laws is difficult. [16]
Barack Obama "Hope" Poster
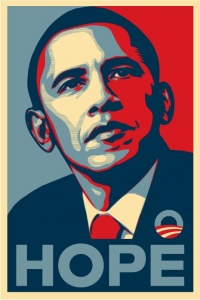
An example of a digital property rights violation that recently occurred was with a "Hope" campaign poster for Barrack Obama. The original source of the photo before the editing was obscured due to the advanced entanglement of digital property circulating the internet. Shepard Fairey, the artist credited with creating the rendition piece, originally discovered the unaltered photo through a quick Google search. The photo was originally published in a 2007 story at Time.com, but was later to be found to have been taken by a photographer named Mannie Garcia in April of 2006 at a National Press Club event. Following the events, Fairey chose to file a declaratory judgement suit against the AP on February 9th, 2008. Later, on March 11th of that same year, AP filed counterclaims. [18]
Legislation
Legislation pertaining to digital property has been poorly defined because it is a developing concept that lacks clear cut legislation like similar property regulations which define tangible and intangible property rights. Digital property legislation fails to define how the transfer, the inheriting, or the selling of digital assets are defined within internet spaces and this is problematic because internet spaces are becoming saturated with notion of the "digital asset".[4] With rapidly evolving technology, and society's cultural and business practices changing in response, the legislative process is slow in comparison. Passing new laws proves to take much longer than the invention of new technological resources and the acceptance of these advancements by society. Legislation not being able to keep pace with rapid innovation in the technology field has resulted in further ethical dilemmas when determining the proper response to conflicts in digital property.
References
- ↑ “State-by-State Digital Estate Planning Laws.” Everplans, www.everplans.com/articles/state-by-state-digital-estate-planning-laws.
- ↑ 2.0 2.1 The Elder Law Report, Vol. XXV, Number 1
- ↑ van Niekerk, A. J Digit Asset Manag (2007) 3: 89. https://doi.org/10.1057/palgrave.dam.3650070
- ↑ 4.0 4.1 Toygar, Alp; Rohm, C.E. Taipe Jr.; and Zhu, Jake (2013) "A New Asset Type: Digital Assets," Journal of International Technology and Information Management: Vol. 22: Iss. 4, Article 7.
- ↑ 5.0 5.1 Lupton, Deborah. “Routledge Handbook of Physical Cultural Studies.” Routledge Handbook of Physical Cultural Studies, London:Routledge.
- ↑ “Did You Know Intellectual Property Is Protected Under the Constitution?” U.S. Chamber of Commerce, 19 Dec. 2017, www.uschamber.com/series/above-the-fold/did-you-know-intellectual-property-protected-under-the-constitution.
- ↑ 7.0 7.1 7.2 “US6314409B2 - System for Controlling Access and Distribution of Digital Property.” Google Patents, Google, patents.google.com/patent/US6314409B2/en.
- ↑ 8.0 8.1 “The Digital Dilemma.” Google Books, books.google.com/books?hl=en&lr=&id=e_GbAgAAQBAJ&oi=fnd&pg=PT22&dq=digital%2Bproperty&ots=cZsvtCwskz&sig=XtBETmEdw61eZhtLXEmQu4NJtnk#v=onepage&q=digital%20property&f=false.
- ↑ “Digital Property Frequqently Asked Questions” American Bar Association, 01 Apr. 2019, https://www.americanbar.org/groups/real_property_trust_estate/resources/estate_planning/digital_property/.
- ↑ “A Helpful Overview Of All Your Digital Property And Digital Assets” Everplans, https://www.everplans.com/articles/a-helpful-overview-of-all-your-digital-property-and-digital-assets.
- ↑ [1]
- ↑ Adams, Anne, et al. “Making Passwords Secure and Usable.” SpringerLink, Springer, London, 1 Jan. 1997, link.springer.com/chapter/10.1007/978-1-4471-3601-9_1.
- ↑ Renaud, Karen, and Verena Zimmermann. “Guidelines for Ethical Nudging in Password Authentication.” SAIEE Africa Research Journal, South African Institute of Electrical Engineers, June 2018, www.scielo.org.za/scielo.php?script=sci_arttext&pid=S1991-16962018000200002&lng=en&nrm=iso&tlng=en.
- ↑ Renaud, Karen, et al. “Lessons Learned from Evaluating Eight Password Nudges in the Wild.” 2017.
- ↑ “Patents, Copyrights and Trademarks – Oh My!” Shenandoah Valley, www.valleysbdc.org/patents-copyrights-and-trademarks-oh-my/.
- ↑ Snapper, John. “The Matter of Plagiarism: What, Why, and It.” The Handbook of Information and Computer Ethics, by Kenneth Einar. Himma and Herman T. Tavani, John Wiley & Sons, 2008, pp. 533–552.
- ↑ Scott, Mac. “Obama Hope Poster - Shepard Fairey (2008).” Medium, FGD1 The Archive, 15 Oct. 2017, medium.com/fgd1-the-archive/obama-hope-poster-by-shepard-fairey-1307a8b6c7be.
- ↑ Fisher III, William W., Frank Cost, Shepard Fairey, and Meir Feder. "Reflections on the hope poster case." Harv. JL & Tech. 25 (2011): 243.