Difference between revisions of "Virtual Private Network"
(→Access Remote Sites) |
(→Access Remote Sites) |
||
| Line 18: | Line 18: | ||
===Access Remote Sites=== | ===Access Remote Sites=== | ||
| − | Using a remote Access VPN, users from across the globe can access a singular private network. <ref>[https://ieeexplore.ieee.org/abstract/document/913204?casa_token=lMFdYdBLousAAAAA:zVQ6DJ3i9yp4lf3goAx8PTO2QyAFAlNRmbyww9TKO3fr363OoWY0Mu1nekH2GolOIl5OTtKkbw “Virtual private networks.” IEEE Potentials, 2001, Accessed 12 Mar.]</ref> This can be used by companies and individuals alike. At the University of Michigan, a VPN is used to allow students to access the Universities encrypted data when not on campus internet <ref>[https://its.umich.edu/enterprise/wifi-networks/vpn “Virtual Private Network (VPN).” University of Michigan, Accessed 12 Mar 2021.]</ref> | + | Using a remote Access VPN, users from across the globe can access a singular private network. <ref>[https://ieeexplore.ieee.org/abstract/document/913204?casa_token=lMFdYdBLousAAAAA:zVQ6DJ3i9yp4lf3goAx8PTO2QyAFAlNRmbyww9TKO3fr363OoWY0Mu1nekH2GolOIl5OTtKkbw “Virtual private networks.” IEEE Potentials, 2001, Accessed 12 Mar.]</ref> This can be used by companies and individuals alike. At the University of Michigan, a VPN is used to allow students to access the Universities encrypted data when not on campus internet. <ref>[https://its.umich.edu/enterprise/wifi-networks/vpn “Virtual Private Network (VPN).” University of Michigan, Accessed 12 Mar 2021.]</ref> This allows students to work remotely on information stored at the university from their home, a conference, or a coffee shop. Throughout the Covid-19 Pandemic, Companies have relied on VPNs to grant employees access to servers, internal applications, and data hosted on site. <ref name="Cloudflare Business VPN"/><ref>[https://openvpn.net/why-companies-are-turning-to-vpns-during-the-coronavirus-outbreak/ “Why Companies Are Turning To VPNs During The CoronaVirus Outbreak.” OpenVPN, 2020, Accessed 12 Mar 2021. ]</ref> These actions were taken to limit the exposure of sensitive data while allowing student and employees access to the information. |
[[File:Vpnvisual.jpg|framed|left|This image shows who cannot see your data when using a vpn. Note that the VPN provider is not on the image<ref>[https://cybersecurity.att.com/blogs/security-essentials/the-ultimate-guide-to-vpn-encryption-protocols-and-ciphers “The ultimate guide to VPN encryption, protocols, and ciphers.” ATT, 31 July 2019, Accessed 25 Mar 2021.]</ref>]] | [[File:Vpnvisual.jpg|framed|left|This image shows who cannot see your data when using a vpn. Note that the VPN provider is not on the image<ref>[https://cybersecurity.att.com/blogs/security-essentials/the-ultimate-guide-to-vpn-encryption-protocols-and-ciphers “The ultimate guide to VPN encryption, protocols, and ciphers.” ATT, 31 July 2019, Accessed 25 Mar 2021.]</ref>]] | ||
Revision as of 22:02, 25 March 2021
A virtual private network (VPN) is a piece of software used to create secure and private connection over a public network.[1] This is achieved by creating a tunnel between the users computer and the target destination. VPNs can be used by both business and individuals.
Main Types of VPNs
There are two main types of VPNs, Site to Site and Remote Access.
Site to Site
A site to site VPN is when a single virtual network is created through multiple local networks.[2] This allows someone to access information from any local network connected to the virtual network while they are on one of the local networks. Once the user is no longer connected to any local network that makes up the virtual network, they are unable to access any of the data. This is due to the VPN Client being hosted on each network rather than a user's device.
Remote Access
Also See: Remote Access
A Remote Access VPN allows a user to connect to a remote server securely. [3] This is done by hosting a VPN client on the users device. By using a remote access VPN, an encrypted 'tunnel' is established. Using this tunnel, the user can then access information only accessible on the local network of the destination, allowing them to interact with files that must be protected.
Commercial VPNs
A Commercial or consumer VPN is a form of the Remote Access VPN model. A commercial VPN uses a remote connection to have the VPN provider interact with websites on the user's behalf, rather than through the user's internet Service Provider. [4] By using a VPN, the I.P address of a user can be hidden from others.
Uses
Access Remote Sites
Using a remote Access VPN, users from across the globe can access a singular private network. [5] This can be used by companies and individuals alike. At the University of Michigan, a VPN is used to allow students to access the Universities encrypted data when not on campus internet. [6] This allows students to work remotely on information stored at the university from their home, a conference, or a coffee shop. Throughout the Covid-19 Pandemic, Companies have relied on VPNs to grant employees access to servers, internal applications, and data hosted on site. [2][7] These actions were taken to limit the exposure of sensitive data while allowing student and employees access to the information.
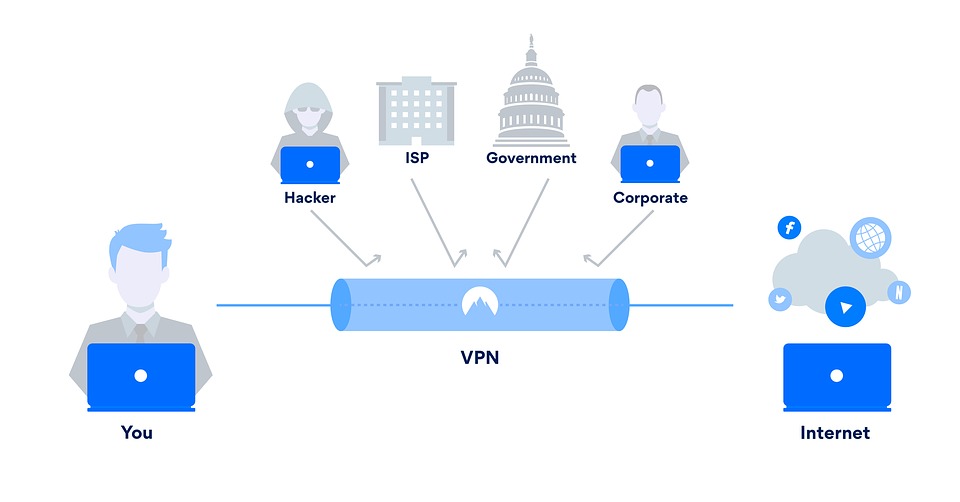
Privacy
As a VPN encrypts the data between the user and a server, a VPN Can help to keep a user's information private.[2] This is similar in use case to accessing a remote site, as the VPN can help a user access data without having to worry about the WiFi network joined. [9] By encrypting the information, the internet provider, government, and others who control the network can see less of what a user is doing online, which can decrease the number of targeted ads, and help to hide a users location. [4]
Access Information From Other Countries
A VPN can also allow a user to access information that is otherwise not available to them by showing that they are in a different location.
Circumventing Government Censorship
By disguising the IP address that a request comes from, a VPN can help to access sites blocked by the government. In China, The Great Firewall is a name given to the censorship of the internet. By using a VPN, Chinese citizens are able to access information that has blocked by the government. [10] This has also allowed Chinese companies to conduct business with overseas partners. As new programs in China seek to limit the internet, a VPN can be a useful tool to circumvent these restrictions. China is not the only where VPNs are used to access blocked content. In Kashmir, people are using VPNs to access social media sites that have been banned. [11]
Streaming Services
One of the most popular features of a VPN is being able to access streaming services that are not available in a given country. Viewers will use a VPN to access Netflix libraries with larger content than their home country. [12]
Ethical Concerns
Most ethical concerns regarding VPN come from the commercial side to the technology.
Pirating of Payed Content
As VPNs can help to mask a user's web access a secrete from their ISP, VPNs are popular tools for torrenting copyrighted material. This has resulted in lawsuits from producers who argue that VPN companies promote and facilitate pirating. [13]
Security of a VPN
Using a VPN does not hide the information being sent from everyone, but instead shifts the ability to see from the user's internet provider to the VPN provider. [15] While VPN Companies claim that they help protect users, the user is still at the mercy of the company for their security. As an example, NordVPN, a leading provider, got hacked in 2019 and did not disclose the hack for months [16]. Users are lead to believe that using a VPN solves all their worries, when in reality their privacy depends on the company they use.
Misleading Advertisements
Several VPN companies have been found to have made misleading claims about their product. In 2019, NordVPN had an Ad banned in the UK when they made false claims suggesting that users without a VPN are broadcasting their passwords to hackers on public WiFi. [17] The Advertising Standards Agency found that the ad made viewers believe that public networks are inherently insecure when this is not true. Other companies have claimed that they keep no logs on user information, but independent investigations have found that several of these companies, including UFO VPN did keep logs. [18]. These misleading claims can be difficult to verify, but by claiming that people are always at risk such as how NordVPN did, and offering a solution, these companies pray on those without the understanding of how they work.
See Also
References
- ↑ Gewirtz, David, and Rae Hodge. “Best VPN service of 2021.” CNN, 19 3 2021, Accessed 25 Mar 2021.
- ↑ 2.0 2.1 2.2 “What is a business VPN?” Cloudfalre, Accessed 12 Mar 2021.
- ↑ “Different Types of VPNs and When to Use Them.” VPNMentor, Accessed 12 Mar 2021.
- ↑ 4.0 4.1 “What is a VPN.” Cloudflare, Accessed 12 Mar 2021.
- ↑ “Virtual private networks.” IEEE Potentials, 2001, Accessed 12 Mar.
- ↑ “Virtual Private Network (VPN).” University of Michigan, Accessed 12 Mar 2021.
- ↑ “Why Companies Are Turning To VPNs During The CoronaVirus Outbreak.” OpenVPN, 2020, Accessed 12 Mar 2021.
- ↑ “The ultimate guide to VPN encryption, protocols, and ciphers.” ATT, 31 July 2019, Accessed 25 Mar 2021.
- ↑ Levin, Benjamin. “A VPN is vital when working from home, so here’s everything you need to know.” CNN, 17 Sept 2020, Accessed 12 Mar 2021.
- ↑ Economy, Elizabeth C. “The great firewall of China: Xi Jinping’s internet shutdown.” The Guardian, 29 Jun 2018, Accessed 12 Mar 2021.
- ↑ Bukhari, Fayaz. “India cracks down on use of VPNs in Kashmir to get around social media ban.” Reuters, 19 Feb 2020, Accessed 12 Mar 2021.
- ↑ Hodge, Rae. “VPN use surges during the coronavirus lockdown, but so do security risks.” CNET, 23 April 2020, Accessed 12 Mar 2021.
- ↑ Sharma, Mayank. “This top VPN is being sued by filmmakers.” Future US, 11 Mar 2021, Accessed 12 Mar 2021.
- ↑ “Popcorn Time VPN.” LiquidVPN, Accessed 25 Mar 2021.
- ↑ Scott, Tom. “This Video Is Sponsored By ███ VPN.” YouTube, 28 Oct 2019, Accessed 12 Mar 2021.
- ↑ Whittaker, Zack. “NordVPN confirms it was hacked.” TechCrunched, 21 Oct 2019, Accessed 12 Mar 2021.
- ↑ Smith, Adam. “NordVPN Ad Banned for Exaggerating Threat of Public Wi-Fi.” PCMag, 1 May 2019, Accessed 12 Mar 2021.
- ↑ Bischoff, Paul. ““Zero logs” VPN exposes millions of logs including user passwords, claims data is anonymous.” Comparitech, 21 July 2020, Accessed 12 Mar 2021.