QR Codes

Contents
Background
History

In 1994, under lead developer Masahiro Hara, the company Denso Wave invented QR codes.[6]. People found that regular barcodes could not store enough information, which led to limitations on their usage.[2] For example, a code 129 barcode, as seen on the right, is a high-density, one-dimensional barcode that can encode letters, numbers, special characters, and control codes. These barcodes can only hold 48 characters of information. Even the most sophisticated one-dimensional barcode can only hold up to 85 characters.[5] In contrast, a QR code can hold up to 7,089 characters— almost 150 times as much information as a one-dimensional code 129 barcode.[6].
Usage
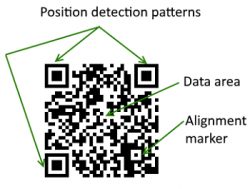
QR codes are read by mobile phones with camera capabilities or QR scanners. Humans cannot manually interpret QR codes, nor can they be read by traditional laser scanners.[8][9] In their article QR Codes in Education, Law and So describe how position detection patterns at three corners of the code are used to read them at any orientation and direction. They describe how QR codes can even be tilted or on a curved surface and still successfully display the information embedded within the code. The device used to read the code then interprets the message and displays information or performs an action on the user's device.[6] QR codes can be used to link to URLs, for payment, to log in to a website, to view a restaurant menu, to display multimedia content, and more.[10]
Types of QR Codes
There are many types of QR codes. The original QR code was called Model 1, able to store up to 1,167 numerals.[11]. The most commonly used version today is the Model 2, with a limit of 7,089 characters.[6] Additionally, there is a smaller version of the standard QR code called the Micro QR code which is limited to 35 numeric characters. Its benefit is in its smaller size, allowing it to be displayed in smaller spaces as compared to the Model 1 and Model 2. Though organizations typically use the Model 2, there are forty different varieties of QR code with distinct data capacities, such as: iQR, Frame QR, Secure QR Code, and LogoQ.[12].
Ethical Implications
QR codes have a variety of uses and can connect users to information very easily and quickly. Since they require minimal technical skills to utilize, they can be applicable to a variety of settings as mentioned above [6]. However, it is crucial to note the ethical implications of QR codes, particularly because they can be used for malicious intent and phishing.
Attackers that intend to override QR codes in some fashion are likely doing it for malicious intent. The most frequently reported attack is social engineering, which is the art of manipulating people to reveal confidential information to the social engineer for the engineer to in turn steal their data [12]. A common practice utilized by these hackers is phishing, which is when the attacker attempts to steal information by impersonating a trustworthy entity [13]. Information that could be stolen could include but is not limited to usernames, passwords, addresses, contacts, and credit card information.
Two Forms of Attack
The two main attack vectors to exploit QR codes are where the attacker replaces the entire QR code and when the attacker modifies individual modules of the QR code [12]. When the attacker replaces the entire QR code, they create a new QR code with a malicious link encoded and paste it over an already existing QR code [12]. The other form of attack involves modifying the encoded content by changing the color of specific modules of the QR Code, where the user will be directed after scanning the code [12].
Twitter Incident 2012

The Jester, a self-described patriotic hacker (@th3j35t3r on Twitter), claimed to have executed a multilayered attack where he broke into mobile phones of various leaders and copied incriminating data [15]. Data is valuable, hence why there are hackers who try to steal it. The Jester’s main targets were English-language websites that recruit followers for al-Qaida (a militant Islamic movement) [15]. To execute his hack, he changed his Twitter profile picture to a QR code. When users went to the website from the QR code, it connected the user to a server network named Netcat [15]. Further, Netcat would see if the user’s device had Twitter and if it was a target phone, then it would send the username to the Jester’s server. The Jester used these usernames to analyze if they were associated with Anonymous news sites and chat rooms, Islamist recruiting sites, and WikiLeaks [15]. Lastly, the Jester would try to steal the data from the targeted phone, which could include messages, call logs, emails, and contacts [15]. This invasion of privacy is unethical and the convenience of making and implementing a QR has potential dangers and harms for smartphone users.
Conclusion of Ethical Implications
While the ethical implications presented could, unfortunately, reveal confidential information to a malicious hacker, QR codes provide a fast and convenient means to give information from one user to the next. Instead of having to type in a long URL, the users can hold their phone over a QR code at any angle for a moment and the link is brought up. The primary challenge associated with harmful QR codes is informing the user of the incident, and it would be beneficial to add a verification process that is transparent to the user and/or warnings to let the user know of possible threats before they enter the dangerous URL or open the media [12].
References
- ↑ Encyclopedia Britannica. (n.d.). QR Code. In britannica.com. Retrieved March 18, 2020, from https://www.britannica.com/technology/QR-Code.
- ↑ 2.0 2.1 Stein, Adriana. (2020, January 1) How QR Codes Work and Their History. QR Code Generator. https://www.qr-code-generator.com/blog/how-qr-codes-work-and-their-history/
- ↑ Luna, N. (2020, July 14). Tech tracker: restaurants are turning to QR codes during the coronavirus pandemic for digital menus and contactless payment. Restaurant Hospitality. https://www.restaurant-hospitality.com/technology/tech-tracker-restaurants-are-turning-qr-codes-during-coronavirus-pandemic-digital-menus
- ↑ http://qrcode.meetheed.com/question7.php
- ↑ 5.0 5.1 Premier Electronics Inc. (n.d.). Barcode Types - Identification and Understanding. Premier Electronics Inc. https://www.premierelectronics.com/blog/barcode-types-identificaton-understanding#
- ↑ 6.0 6.1 6.2 6.3 6.4 Law, Ching-yin and So, Simon (2010) QR Codes in Education. Journal of Educational Technology Development and Exchange (JETDE): Vol. 3 : Iss. 1 , Article 7. https://aquila.usm.edu/cgi/viewcontent.cgi?article=1011&context=jetde
- ↑ https://www.cgap.org/blog/inside-qr-codes-how-black-white-dots-simplify-digital-payments
- ↑ Rouillard, José. (2009, October 11). Contextual QR Codes. 2008 The Third International Multi-Conference on Computing in the Global Information Technology (iccgi 2008), Athens, Greece, 2008, pp. 50-55. https://ieeexplore.ieee.org/stamp/stamp.jsp?tp=&arnumber=4591344
- ↑ name="Premier"
- ↑ QR Code. (2021, February 7). Wikipedia. https://en.wikipedia.org/wiki/QR_code
- ↑ Chang, Jae Hwa. (2014, July 30) An introduction to using QR codes in scholarly journals. Science Editing. https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.986.6494&rep=rep1&type=pdf
- ↑ 12.0 12.1 12.2 12.3 12.4 12.5 Krombholz K., Frühwirt P., Kieseberg P., Kapsalis I., Huber M., Weippl E. (2014). QR Code Security: A Survey of Attacks and Challenges for Usable Security. Human Aspects of Information Security, Privacy, and Trust. https://link.springer.com/content/pdf/10.1007%2F978-3-319-07620-1_8.pdf
- ↑ Jagatic, T., Johnson, N. et al. (2007, October). Social Phishing Volume 50 Issue 10. Communications of the ACM. https://dl.acm.org/doi/fullHtml/10.1145/1290958.1290968?casa_token=aKPSW2sVqnMAAAAA:OH7v7hXko3P8lyga-GNd8zQMqD_AS_QcAULLPg3M7Ln17OeJ9uLZHogaIJhtgc97saukLp3-A8up
- ↑ https://twitter.com/th3j35t3r
- ↑ 15.0 15.1 15.2 15.3 15.4 Wagenseil, Paul. (2012, March 13). Anti-Anonymous hacker threatens to expose them. NBC News. SecurityNewsDaily. https://www.nbcnews.com/id/wbna46716942