Message-Delivery & Seen-Status Tracking (A.k.a Read Receipts)
A read receipt, or return receipt, is a notification, indicative of seen status, returned to the sender of a message once the receiver has opened said message and use various forms of delivery-tracking technology to identify data. Often this technology is inaccurate, especially in emailing. Whether it's accurate or not, the tech can be intrusive of receivers' private information and presents an ongoing and widely disputed debate due to the shear amount of information that can be picked up by data-trading organizations. Princeton researchers revealed in 2017 that there has been very little research done on email tracking, despite the vast focus on revealing the technology behind web tracking. Because of the lack of research and heavily debated methodology behind its use, this Wiki article explores the information publicly known on the subject. This article will reveal the gears and functionality behind message-delivery and seen-status tracking software, as well as the legal implications and invasion of privacy in its use across various forms of digital messaging.
History
Instant Messaging's delivery tracking and SMS's receipt-sending software have been around for a long time, with email trackers going back even farther in history. As Guinness World Records points out, the first email correspondence was made in 1971 by Ray Tomlinson, a computer engineer, when he sent "QWERTYIOP or something similar" to another computer he was working on. Tomlinson successfully built the software while working for the United States Defense Department building a message service in ARPANET using Cambridge's early computer tech.[1]
Long after this breakthrough, various parties began building web mail in 1993.[2] The introduction of web mail allowed for companies to add emailing to web browsers. Since web browser technology was so robust at the time, and would only continue to grow, email creators had a new toy—HTML. The addition of HTML, CSS, and other web programming technologies was a game changer for marketing and intelligence departments. These programs support image and file embedding on browsers. By writing and sending emails using these browser programs and only a tiny chunk of code, various government organizations, companies, and unidentifiable parties were able to privately create and implement a secret and intrusive method to track email data. This method was called Tracking Pixels and it is still used in email today. The tracking technology was unknown to the mass public until Hewlett-Packard, the global information and computer hardware company often referred to as HP, screwed up by inadvertently releasing their secret affairs in 2006.[3] HP partnered with a company named Read Notify who developed a powerful and reliable program that used 36 different methods to track information, a few of which used tracking pixels for email tracking. ReadNotify was used by HP to track a scandalous email leaked to press. The technology was revealed in HP's lawsuit that followed and spread shock amongst the tech community and email users that their private emailing habits could be tracked.
Email tracking publicized beyond various private companies and governmental organizations, beginning to gain traction in marketing departments and more insidious parties. Meanwhile, SMS text messaging had been around since 1992 and now thriving globally.[4] By this time, billions of text messages had been sent across the world and Twitter had just announced that they were breaking into the SMS sphere to begin working on Instant Messaging capabilities.[5] It didn't take long for email tracking companies to encompass a new medium to track. In turn, SMS tracking was born. SMS trackers became programs that track the delivery and content of both text and pictures within text messages.[6] Phone service companies and third-party companies eventually publicized and implemented programs that deliberately sent tracking information between messages that could be turned on and off by the users (depending on the service). This tech was typically referred to as return receipts. Return receipts were able to be controlled, tracked, and alerting by the user in some email clients, but many were made secret. With return receipts implemented in many carriers and tracking technology ominously in development elsewhere, return receipt programs offered sender and receiver information on a silver platter to third-party tracking technologies.
Shortly after email and SMS/MMS trackers and receipts were developed, in 2011, in came Apple with iMessage Instant Messaging service installed from the beginning with an end-to-end encrypted version of return receipts officially deemed "read receipts."[7] By allowing each user to toggle tracking on or off, Apple developed a system that benefited both users who exchanged information by indicating read status without expelling sensitive information outside those two channels. A company that was able to fully encrypt delivery and tracking data sparked the most significant security leap in return receipts for the common consumer. Apple and other companies' encrypted message tracking and receipt breakthroughs stoked a small flame into a roaring debate to decide whether the use of tracking technology is ethical. so that it's now a debate whether users should even evade privacy in fully encrypted Instant Messaging services now used today.
Technologies & How It Works
Email Tracking
Delivery tracking is nowadays used in Instant Messaging (IM), Short Message Service (SMS) and Multimedia Messaging Service (MMS), but originally began with email tracking software.[8] Email tracking technology was limited to monitoring delivery status before the introduction of “seen”-status tracking. Depending on the platform used and method that receipts are fetched, other robust forms of data points can be obtained using more modern code that track the receiver’s Internet Protocol (IP) address. Beyond the status of whether the message has been seen by the receiver, the notification returned to the sender may include embedded information like reception time, the time that the message has been opened, and location data indicating the receiver’s continent, country, state, city, zip code, or even rough coordinates within a multi-square-mile radius of where the message was opened from your IP address and other embedded email information.[9]
The most common and arguably most effective way to fetch IP address is through pixel tracking, installing a tiny 1x1 pixel image into an email that can then be fetched for data once downloaded from the server in an opened email.[10] This trojan horse can send back the IP address, as well as other content about the receiver's computer and the network it's running on.
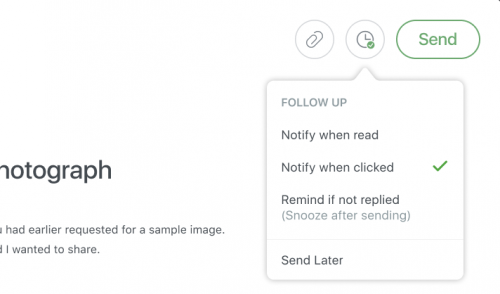
In emailing, return receipts can also be sent to other inboxes with both sender and receiver controls to be toggled on and off. These receipts that are embedded in the email can even notify the sender when an external link in an email was clicked. Some current email clients can enable and disable this tracking, but cannot always control its accuracy. Because of the power and privacy concerns that these tracking capabilities have, free services like Gmail don't offer tracking for users unless limited to the confines of users emailing within a certain organization. Products like Newton and Superhuman have cutting edge read receipt and delivery tracking protocols embedded into their programs that allows their users to fetch information from their email receivers outside immediate organizations and users on the same email client.
SMS/MMS Tracking
As Twilio explains, SMS/MMS uses a different process than email tracking. Conversations are tracked by installing cookies into phone numbers. As long as both phone numbers in a correspondence have installed cookies, then message data may be tracked. The messages can also be tracked via the network.[6] The carrier has access to the network since they own it and third parties may be able to tap into this network externally to gain access to tracking data. Return receipts function differently than external tracking. Receipts are sent deliberately to the receiver so that the receiver's program may track these protocols.
Instant Message Encryption
Encrypted instant messaging is encrypted end-to-end, which means that each user's messaging protocols in a correspondence encrypt sent messages and decrypt received messages with the same code. Receipts are sent within these encryptions, so although data is sent about each user, the data is limited to the sender and receiver only, no exceptions.[11] Instant messaging is used in products like Apple iMessage, Facebook Messenger, WhatsApp, and Signal.
Reliability
Read receipts can provide both highly accurate and highly inaccurate data. Read receipts in email especially have multiple reasonings to fail. Read receipts may be deactivated by the internal software built by an organization to manage how email is received and sent. Other ways could be technical error in sending or receiving an email. Some email services also allow the user to manage the settings and controls behind how read receipts are used and how certain data is tracked.
The Internet Engineering Task Force (IETF) explains that even through Internet protocols, tracking may get lost in transit. The IETF is an organization that develops and regulates protocols for securely packaging and transporting messages across the Internet.[12] These protocols are called Message Disposition Notifications (MDNs). The IETF indicates the lack of reliability and high fluctuation rate of tracking software’s success in Message Disposition Notification RFC 3798: “MDNs may be forged as easily as ordinary Internet electronic mail and whilst they can provide valuable information to the mail user, they cannot be relied upon as a guarantee that a message was or was not seen by the recipient. Even if MDNs are not actively forged, they may be lost in transit.”[13]
Google itself explains that Gmail's email tracking is not always reliable. A support page explains that you should not rely on receipts to certify delivery because the delivery-tracking system fails or creates miscommunication, especially when functioning with other email clients. Getting a read receipt also doesn't necessarily mean that the recipient read the sender's message. The way a receipt works depends on which email system the recipient uses to collect emails. For example, a sender may get a read receipt if a person using an IMAP-based email client intentionally marks an email message as read using the inbox view without opening the email. Some non-IMAP mobile email systems may not return read receipts at all. As another example, a failed receipt could be due to the receiver's settings. If the sender uses an email with a tracking pixel, the recipient will open the email and notify the sender with a timestamp of that interaction and the other IP information the tracking pixel picks up. However, what the sender doesn't know is that the email server of the recipient has their image preview functions disabled. This would prevent the sender from receiving any data after the recipient opens the email because the pixel will never be activated from the sender's server.[14]
In SMS/MMS, read receipts most often fail when service bandwidth prevents a message from sending in full. However, since Instant Messages are secured packages of data sent over a stable networks, these packages rarely break apart.
Tracking accuracy is dependent on the platforms used in exchanging read receipts. Some products function better than others, especially with internal end-to-end encryption like Apple iMessage. Other software, like email tracking, often fails to scrape IPs correctly and return the data successfully. Due to pixel tracking, it is still much easier to discretely track information in an email than it is with carrier-regulated SMS/MMS. However, end-to-end encrypted Instant Messages are nearly impossible to decipher, even for the network carrier and device maker, making them unequivocally reliable from a technological point of view. Although encrypted Instant Messaging is fully reliable given that the data is transformed into unintelligible chunks of information in transport, users still need to be cautious of what the receiver could do with the sender's data and ensure on the reliability of who they are sending private information in tracking receipts to.[15] Due to the inaccuracies of unencrypted tracking technologies and the unreliability of humans, these programs reveal two things: the ethical implications behind the lack of revelation to what may or may not be true in users' data transference when the technology's success rate fluctuates, and how the individuals themselves may interpret correct and incorrect information relayed in a correspondence.
Legal Challenges
By default, email is naked of legal protection. If you wrote a paper letter for someone, sealed it in an opaque envelope and mailed it out to someone, the content is legally protected and binding to you and the recipient. Others would need a search warrant issued on probable cause to search that envelope. Beyond telephone calls, digital communications unprotected by specific organizations (not including messaging that occurs between organizations) has very little, or even zero, forms of legal protection.
Email for instance is a unprotected in transit. Once an email is stored on a computer, it is protected from unauthorized use and access by the Stored Communications Act[16] In transit though, legally speaking, email is not protected. Anyone is legally able to access an email. One must also consider that access is only revoked for unauthorized use. If the content within an email is embedded before sending, then it is authorized at "send." This means that anyone who is partnered with the sender in handling the embedded tracking information before sending the email, they are an authorized user after the email is received. However, there is no way to track these partnerships if made discretely because there is no "sign here" line embedded in an email.
SMS/MMS, on the other hand, have more laws set in stone. Most of these laws fall under the Telephone Consumer Protection Act (TCPA) of 1991 that regulates the way marketers are allowed to access telephone numbers.[17] Hackers are forbidden and marketers are restricted to user consent to "opt out."
Since Instant Messaging is controlled by companies' internal networks, each company has its own legal terms in data transfer.
Are tracking receipts legally binding?
Read receipts do not provide reliable proof of email delivery due to their poor success rate across multiple platforms (see reliability section above), making them unable to count as legal evidence.[18] However, this doesn't mean that the tracking receipt won't expose other information that is legally standing in a court case. For instance, in HP's legal case mentioned early, the tech company used tracking technology to identify certain personal information to the reporter they bugged. Use of the tracking technology was not illegal, but the attempt at what they desired to retrieve was.
Legally Protect Tracking
Despite receipts being naked of legal standing, court cases are of course still raised. To protect read receipts, email users can pay for email clients like Newton or Superhuman to securely send and receive intentionally legally binding tracking receipts. Other email extensions like eEvidence certifies message delivery with legal validity to ensure that the sender has full rights to delivery receipts.[19]
Tech Cannot Define Recipients' "True" Read Status
In the end, an email's read status still can't be guaranteed without response because there is no way of knowing whether the recipient actually saw and read the opened message without wildly illegal hacking. The IFTF and Google don't recommend relying on read receipts for successful email tracking because there is more than just the accuracy of the technology, but the fact that the tech may have worked, but the human may still not have read or interacted with the email.
What are the stakes of unreliable tracking data?
Since read receipts do not stand in court, stakes are low. However, if the tracking technology finds other information that is either true or untrue, it could present false or scandalous information when cross-referenced with other collected data that's confirmed to be true. This may ruin the reputation of individuals or companies. Being that information spreads so quickly now, there is also risk that reputations could be ruined purely based on the whim that something is correct in collected data. See privacy below to see how these technologies can connect to identify deeper information than an IP address.
Privacy Concerns
Email alone can provide a decent amount of information about a user. By collecting one's IP address, an email can provide enough data to then be used to connect and access other data in the sending-party's records. Check your own IP address on iplocation.net to get a glimpse of what your IP alone can tell others about you. On top of collecting information from email, specifically through IP addresses, many external programs may also be used to identify and connect personal information. This is most commonly done via partnerships with other parties.
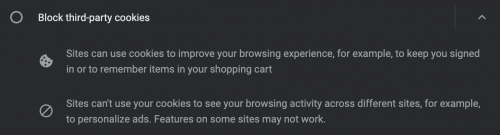
What some may consider an egregiously sized breach of privacy, a significant amount of private, identifiable information may be obtained from users depending on the existence of external partnerships with the sender of an email. Browsers collect cookies. Apps collect other forms of data. Some of the cookies placed in browsers may be fully accessible to be collected by other organizations. Khan Academy explains the two common forms of data placing and fetching in browsers called first-party and third-party cookies. First-party cookies are used by the visited site in a browser when visiting said site directly. Third-party cookies may be placed in someone's browser by sites partnered with the visited site which can provide trackable data on user history to these partnered websites.[20] If other companies or suspicious individuals have information-sharing agreements with the interacted website, third-party cookies may be sent to a user's browser cache and provide this tracking data to partnered parties to then be tied to other data.[21] These agreements can grant others access to a user's information using external processes to email sharing called UID2. UID2 is a series of protocols that can be used to collect, analyze, and share users’ personally-identifying information that can be used in connecting email addresses, IP addresses, cookies, and other identifiable technologies that identify users and their other private information.[22] Correlations of data on a single user can then be made between third-party, cookie-placing agreements from a browser or app and the pixel-tracking and IP-scraping technologies installed in the email a user may open. Unless cookie collection is turned off in browsers, a firewall is used, and the user has tracking turned off using a robustly built email client, the user has no control over who can breach their privacy by collaborating externally to merge identifiable data and collect information about them.
The best method to prevent the majority of one's data from being collected, analyzed, and connected together to develop a persona of data is to use a VPN, blocking IP collection on email and browsers and corrupting much—not all—cookie collection.
References
- ↑ "1971: First Ever Email," Guinness World Records (Rachel Swatman), https://www.guinnessworldrecords.com/news/60at60/2015/8/1971-first-ever-email-392973
- ↑ "How did email grow from messages between academics to a global epidemic?, The Guardian, https://www.theguardian.com/technology/2016/mar/07/email-ray-tomlinson-history
- ↑ "How HP bugged e-mail," CNET Tech (Joris Evers), https://www.cnet.com/tech/services-and-software/how-hp-bugged-e-mail/
- ↑ "The First Text Message Celebrates 25 Years," NPR, https://www.npr.org/2017/12/04/568393428/the-first-text-messages-celebrates-25-years#:~:text=Transcript-,The%20first%20text%20message%20was%20transmitted%20Dec.,of%20Vodafone%20director%20Richard%20Jarvis.
- ↑ "The text message turns 20: A brief history of SMS," The Week, https://theweek.com/articles/469869/text-message-turns-20-brief-history-sms
- ↑ 6.0 6.1 "SMS Tracker," Twilio, https://www.twilio.com/docs/glossary/what-sms-tracker
- ↑ "What is the difference between iMessage and SMS/MMS?," Apple, https://support.apple.com/en-us/HT207006#:~:text=If%20you%20aren't%20using,need%20a%20text%2Dmessaging%20plan.
- ↑ "What is SMS & MMS?," T-Mobile, https://www.t-mobile.com/resources/what-is-an-SMS
- ↑ "What does an IP address tell you and how it can put you at risk?" Norton, https://us.norton.com/internetsecurity-privacy-what-does-an-ip-address-tell-you.html#:~:text=What%20information%20does%20my%20IP,or%20other%20precise%20personal%20information.
- ↑ "Email tracking pixels 101: How do they work and why are they used?" Nutshell (Maria Waida), https://www.nutshell.com/blog/email-tracking-pixels-101-how-do-tracking-pixels-work
- ↑ "How end-to-end encryption in Messages provides more security," Google, https://support.google.com/messages/answer/10262381?hl=en#:~:text=How%20end%2Dto%2Dend%20encryption%20works,decoded%20with%20a%20secret%20key.
- ↑ "Use of Message Disposition Notifications," IBM, https://www.ibm.com/docs/en/b2b-integrator/5.2?topic=higher-use-message-disposition-notifications
- ↑ "RFC 3798," IETF, https://datatracker.ietf.org/doc/html/rfc3798
- ↑ "Request or return a read receipt," Google, https://support.google.com/mail/answer/9413651?visit_id=637395923678980799-3760639549&hl=en&rd=2
- ↑ "Encrypted Messaging Isn’t Magic," Wired, https://www.wired.com/story/encrypted-messaging-isnt-magic/
- ↑ "Conducting Cybersecurity Research Legally and Ethically," University of California, Berkeley School of Law (Aaron J. Burstein), https://www.usenix.org/legacy/event/leet08/tech/full_papers/burstein/burstein_html/index.html
- ↑ "Text Messaging Laws Every Business Has To Know About," Textedly (Jessie Chantel), https://www.usenix.org/legacy/event/leet08/tech/full_papers/burstein/burstein_html/index.html
- ↑ "Email Tracking: Read Receipts Are Not Reliable Proof To Prove Email Delivery," eEvidence, https://blog.eevidence.com/en/email-tracking-read-receipts/
- ↑ "eEvidence, eEvidence, https://try.eevidence.com/registeredemail/?utm_source=blog&utm_medium=blogpost&utm_campaign=readreceipts
- ↑ "Web Cookies," Khan Academy, https://www.khanacademy.org/computing/computers-and-internet/xcae6f4a7ff015e7d:online-data-security/xcae6f4a7ff015e7d:user-data-tracking/a/web-cookies
- ↑ "How to Surf the Web Anonymously," How Stuff Works, https://electronics.howstuffworks.com/how-to-tech/how-to-surf-the-web-anonymously.htm
- ↑ "After Cookies, Ad Tech Wants to Use Your Email to Track You Everywhere," EFF, https://www.eff.org/deeplinks/2021/04/after-cookies-ad-tech-wants-use-your-email-track-you-everywhere