Information Security
Information Security is the process of protecting information from unintended access by others. The methodologies for protecting information varies based on the type of information being protected, to whom the information currently belongs, and how the information could potentially be utilized by others.
Concern with the security of information has become more concentrated with the proliferation of electronic information storage mechanisms, and subsequently with the spread of information in an online environment. [1] These mediums of information transportation have both helped and hindered the process of data protection. For instance, by allowing information to be encrypted and decrypted in a complex manner when being transferred from one point to another, data can be protected in a more robust way. Conversely, the ease with which information can be copied and disseminated without expressed consent of the information-holder can cause it to be used in nefarious ways.
Information is linked explicitly with privacy in the case of an individual. Without protecting an individual's private information, they can be subject to identity theft. It is thus a moral and often legal obligation that companies provide security to the information of their clients.[2]
Contents
Conceptual Overview
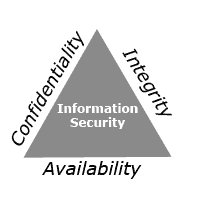
Protecting private information is important to ensure that information is both reliable and confidential. When information is not protected in most formats, it can be tampered with causing inaccuracies or discrepancies. If the information is valuable and is not protected, it can be distributed to parties that could cause harm to it in some way. The CIA Model of Information Security (Confidentiality-Integrity-Availability) [3] is a fundamental way of describing the steps necessary for protecting information.
Information Confidentiality
The process of ensuring that information is available only to those who are authorized to view it. Disclosure of parts, or the entirety of sensitive information can harm those to whom the information belongs, as well as the inherent value of the information itself. Authentication methods IDs, passwords, pons, etc, reinforces what confidentiality is good for.
Information Integrity
Also called information reliability, it is of the utmost importance that information is accurate, up-to-date, and complete for those who plan to use it. Protecting information against unwanted modification or destruction is a significant part of securing information.
Information Availability
Providing access to protected information in both a timely, reliable manner helps those who are monitoring it and using it to discover issues or changes in the information itself.
Information Security and Electronic Storage
The advent of data-transfer via electronic means on the internet has shifted the focus of information security from physical protection (protecting the actual medium the information is stored on) to a more broad definition of what protection means. Prior to computerization of data, often the easiest way to protect information was to reduce access to the physical medium on which the information was kept. This could be done by managing who could access the stored mediums where the information was kept (ie. determining who could access a filing cabinet with important paperwork). The low-cost of information replication in an electronic format, and the difficulty of identifying who is viewing information has greatly changed the ways in which information needs to be protected.
Access Controls
The foremost step in identifying who a potential information user is before allowing them to view or manipulating data in an electronic environment. [4] Creating profiles of a user's identity can be a first step in allowing them access to sensitive information. These profiles can then be protected with unique passwords that allow data-protection systems to authenticate their identity before allowing them to access information. An individual's behavior while using information can also be monitored by connecting their actions to a unique profile.
Data Encryption
Information can be protected when it is being transferred from point-to-point by using processes to encrypt, or jumble, the data while in transit, and then re-assemble it upon arrival at its destination. Also called cryptography, the process of encrypting and decrypting data between two points using a shared key is a way of providing information security.
Ethics of Information Privacy
Determining social expectations for protecting information is a societal-wide undertaking. Without a common notion of what protecting information entails, an individual's personal data can easily face unnecessary jeopardizing circumstances. Generally, protecting important personal information is a necessity defined by a society at large. As a result of these common beliefs on information security, the current practice in most Western societies is that companies and individuals must jointly undertake the responsibility of protecting an individual's personal information in order to prevent it from being misused.
It is also important to note that protecting information is not a one-time occurrence that must only be undertaken when data is created or stored; it is an iterative process that exists during the entire existence of every piece of information. As information is subject to change, the methods by which it needs to be protect are also subject to change over time.
Individual Information Privacy
The security of an individual's personal information is necessarily tied to their personal privacy. When an individual interacts with other parties when using their private information, especially in the online environment, it is hard to guarantee that this information will retain its security. Companies have a legal obligation within the United States to provide protection of personal information provided during a business transaction to their customers, especially in an online environment. [5]
See Also
- Cyber Law
- Information Ethics
- Information Transparency
- Online Identity
- Online Identity Theft
- Virtual Environment
References
- ↑ Overview of Information Security and Systems Development
- ↑ [1] Gerber, M., & von Solms, R. (2008). Information security requirements – Interpreting the legal aspects. Computers & Security, 27(5-6), 124-135. doi:10.1016/j.cose.2008.07.009
- ↑ CIA Information Security Model
- ↑ Access Controls
- ↑ Federal Trade Commission Identity Protection Act