Virtual Private Network
WORK IN PROGRESS ------------------------------------------------------------------------------------------------------------
A virtual private network (abbreviated VPN) is a technology used to create a safe and private connection over a public network.[1] This is achieved by controlling internet traffic between the user's computer and the destination so the location of the user's computer is hidden or it appears that they are working from somewhere other than their true location.[2] VPNs can be used by both businesses and individuals.
Contents
History
The first VPN was developed in 1996 by Microsoft software developer Gurdeep Pall. It was created as an efficient way for employees to access company data securely from remote locations, and was built on Point-to-Point Tunneling Protocol (PPTP), a method still in use. [3]
Over time, VPNs grew beyond a process of employees working from home to much broader uses. Today, one of the most common applications is in the form of Transport Layer Security (TSL), or its predecessor Secure Sockets Layer (SSL) encryption. This is a feature of the majority of webpages on the internet, often indicated with a lock icon in the browser’s search bar and labeled as “Connection Secure.” [4]
Types of VPNs
Different types of VPNs come from varying strategies of redirecting and masking internet traffic. There are two primary types of VPNs: Site-to-Site and Remote Access.[5]
Site-to-Site
A Site-to-Site VPN, also called a Router-to-Router VPN, occurs when at least one user's network connects to another.[5] According to cybersecurity company Fortinet, these types of VPNs are often found in business settings. These routers connect to essentially form one large network comprised of local networks.[6] This allows someone on one of the local connections to access information from any of the other local networks connected to the VPN. One subtype of this category is an Intranet-Based Site-to-Site VPN. Intranet-Based Site-to-Site VPNs are often used within a company when the flow of information is relatively free. That is, all networks involved in the VPN have equal access and sharing of all resources. This helps simulate the experience of everyone working on the same local network.[6][5] Conversely, Extranet-Based Site-to-Site VPNs are used for more selective sharing.[6] GeeksforGeeks, a popular educational programming website, describes them as "companies [using] ... VPN ... to connect to the office of another company."[5]
Remote Access
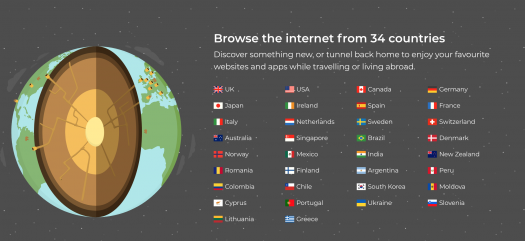
With a Remote Access VPN, rather than connecting to another router, the user connects securely to a remote network.[7] By using a remote access VPN, an encrypted "tunnel" is created from the user's location to the VPN destination. This destination is determined by the creator of the private network being accessed, and some VPNs allow the user to choose their destination.[2] TunnelBear is an example of a VPN service where the user is able to choose where they would like to "tunnel" their data.
Types of VPN Protocols
A VPN protocol is a set of rules or instructions that will determine how your data routes between your device and the VPN server. VPN providers rely on protocols to ensure a stable and secure connection. VPN protocols have unique specifications that offer benefits to the VPN user based on the circumstances. Some specialize in privacy while others put an emphasis on speed. VPNs utilize different protocols depending on the device being used, what you want to do, and how you want to do it. [9]
Internet Protocol Security (IPSec)
An IPSec is used to secure internet communication across an IP network. IPSec secures internet protocol communication by verifying the sessions and encrypts each data packet during the connection. [10]
Point-to-Point Tunneling Protocol (PPTP)
Point-to-point tunneling protocol is one of the oldest VPN protocols in existence. A PPTP generates a tunnel and confines the data packet. [10] The point-to-point part of the protocol refers to the connection created by PPTP. It allows one point (user computer) to access another specific point (remote network) over the internet. The tunneling part of the protocol refers to the way one protocol is encapsulated within another protocol. In PPTP, the point-to-point protocol is wrapped inside the TCP/IP protocol, which provides the internet connection. [11]
OpenVPN
OpenVPN is an open-source protocol that allows developers access to its underlying code. This protocol has grown in popularity due to its use of (virtually unbreakable) AES-256 bit key with 2048-bit RSA authentication and a 160-bit SHA1 hash algorithm. [12]
Secure Socket Tunneling Protocol (SSTP)
An SSTP is popular due to its full integration with every Microsoft operating system since Windows Vista SP 1. It utilizes 2048-bit SSL/TLS certificates for authentication and 256-bit SSL keys for encryption which provides good security. [13]
Uses
Access Remote Sites
Using a remote access VPN, users from across the globe can access a singular private network.[14] At the University of Michigan, a VPN is used to allow students to access the University's encrypted data when not on the campus internet. This allows students to remotely access information stored at the university, such as databases, or to take advantage of network protection provided through the university.[15] Throughout the Covid-19 pandemic, companies have relied on VPNs to grant employees access to servers, internal applications, and data hosted on-site. These actions were taken to limit the exposure of sensitive data.[16][17]
Privacy
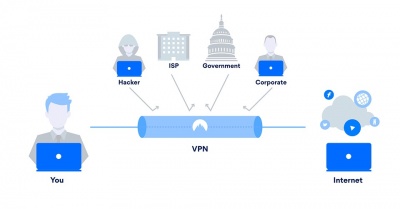
As a VPN encrypts the data between the user and the network, it can help keep a user's information private.[16] This functionality is similar to how VPNs are used to access remote sites, as they help a user access data without having to worry about the WiFi network they're connected to.[19] By encrypting the information, the internet provider, government, and others who control the network can see less of what a user is doing online. Not only does this limit what data is collected about the user, but it can also decrease the number of targeted ads and help to hide the user's location.[20]
Accessing Information From Other Countries
A VPN can also allow a user to access region locked content or information that would otherwise be unavailable by making it appear as if they are located in a different location.
Circumventing Government Censorship
By disguising the IP address that a request comes from, a VPN can help to access sites blocked by the government in the country where the user is located. In China, "The Great Firewall" is a name given to the country-wide censorship of the internet. By using a VPN, Chinese citizens are able to access information that would otherwise be restricted by their government.[21] This has also allowed Chinese companies to conduct business with overseas partners. As new programs in China seek to control internet usage, some argue that VPNs can be useful tools to avoid these restrictions.[22] China is not the only location where VPNs are used to access blocked content. In Kashmir, citizens use VPNs to access social media sites such as WhatsApp or Instagram that have been banned by the government.[23]
Streaming Services
Another common use for a VPN is accessing streaming services that are not available in a given country. Viewers use VPNS to access the libraries of these services, primarily Netflix, by changing their virtual location to that of another country that has the desired content.[24] For example, as of November 2020, Star Trek: Discovery was not available on Netflix in the US and Canada but was in other countries.[25] In 2016, Netflix began taking steps to prevent the use of VPNs, though the CEO described the number of VPN users to be “really inconsequential.” [26] They did this by comparing the location of the user's IP address (which the VPN has altered) and their Domain Name Server (DNS) which could still reveal the user's true location.[27]
Netflix’s measures have reduced the general effectiveness of VPNs, rendering many services incompatible. However, there are still a multitude of options available that still bypass the region locking of the platform Hochstadt, Ariel. "8 Best Netflix VPNs That Still Work Reliably [Tested in 2021." vpnMentor, 5 April 2021, https://www.vpnmentor.com/blog/5-best-vpns-netflix-actually-work/. Accessed 10 April 2021.]</ref>
The 5 Eyes, 9 Eyes, and 14 Eyes Agreements
After World War II, the United States and the United Kingdom signed the BRUSA Agreement to share intelligence between the two countries. (The BRUSA Agreement is now known as the UKUSA Agreement.[28] Over time, this agreement grew to include more countries, eventually leading to the 5 Eyes, 9 Eyes, and 14 Eyes agreements (each one involving a different group of countries).
The initial intent of these agreements was to gather intelligence on the Soviet Union. The member countries of the official 5 Eyes treaty included the United States, Canada, the United Kingdom, Australia, and New Zealand. In 1982, the 14 Eyes group was formed, consisting of Germany, Italy, Spain, France, Sweden, the Netherlands, Norway, Belgium, and Denmark on top of the existing members of the 5 Eyes treaty. 9 Eyes is not outlined in a specific treaty, but consists of the 5 Eyes members plus Denmark, Norway, France, and the Netherlands. [29]
As a part of this agreement, any intelligence gained by one country is automatically shared with all other countries in the agreement.[30] Some VPN companies, such as Restore Privacy, highlight this arrangement in support of using their services, claiming that they can help users escape government surveillance and information sharing between countries with these agreements.[31]
Ethical Concerns
Most ethical concerns regarding VPNs come from the commercial uses of the technology.
Pirating of Paid Content
Since VPNs can help make a user's web access history a secret from their Internet Service Provider (ISP), VPNs have become popular tools for illegally obtaining copyrighted material. This has resulted in lawsuits from producers who argue that VPN companies promote and facilitate pirating.[32] One popular method of pirating material like this is "torrenting" copyrighted material like movies, music, or video games. "Torrenting" refers to a method of peer-to-peer file sharing that uses the BitTorrent protocol. VPNs are often used in conjunction with this method because it hides the illegal file sharing activity from Internet Service Providers.[33]
Security of a VPN
Using a VPN does not hide the information being sent from everyone, but instead shifts the ability to see the information from the user's internet service provider to the VPN provider.[35] Some argue, however, that VPNs are not completely safe because the user is still dependent on the VPN company for their security. As an example, NordVPN, a leading provider, got hacked in 2019 and did not disclose the hack for several months.[36]
According to M.T. Khan and others, users rely on virtual private network services for a number of reasons: to preserve their privacy, circumvent censorship, and access geo-filtered content. A 2018 evaluation of sixty-two commercial VPN providers showed that while the services seem less likely to intercept or tamper with user traffic, some VPNs do leak user traffic through a variety of means. From the study, in 10% of the providers studied, between 5 and 30% of the VPNs appeared to be hosted on servers located in countries other than those advertised to users.[37] Perta et al. analyzed fourteen of the most popular commercial VPN services in 2015 and inspected their internals and infrastructures. They found that the majority of VPN services suffer from IPv6 traffic leakage. A sophisticated DNS hijacking attack would allow all traffic to be transparently captured. [38]
Misleading Advertisements
Several VPN companies have been found to have made misleading claims about their product. In 2019, NordVPN had an advertisement banned in the UK when they made false claims suggesting that users without a VPN are broadcasting their passwords to hackers on public WiFi. The Advertising Standards Agency found that the ad incorrectly made viewers believe that public networks are inherently insecure.[39] Other companies have claimed that they keep no logs on user information, but independent investigations have found that several of these companies, including UFO VPN, have kept logs.[40].
See Also
References
- ↑ Gewirtz, David, and Rae Hodge. “Best VPN service of 2021.” CNN, 19 Mar. 2021, www.cnet.com/news/best-vpn/. Accessed 25 Mar. 2021.
- ↑ 2.0 2.1 Symanovich, Steve. "What is a VPN?" Norton, 14 Jan. 2021, us.norton.com/internetsecurity-privacy-what-is-a-vpn.html. Accessed 8 Apr. 2021.
- ↑ "A Brief History of VPNs." vypervpn, 21 June 2016, https://www.vyprvpn.com/blog/brief-history-of-vpns. Accessed 10 April 2021.
- ↑ Rosencrance, Linda. "SSL VPN (Secure Sockets Layer virtual private network)." SearchSecurity, April 2020, https://searchsecurity.techtarget.com/definition/SSL-VPN. Accessed 10 April 2021.
- ↑ 5.0 5.1 5.2 5.3 "Types of Virtual Private Network (VPN) and its Protocols." Geeks for Geeks, 10 Apr. 2019, www.geeksforgeeks.org/types-of-virtual-private-network-vpn-and-its-protocols/. Accessed 8 Apr. 2021.
- ↑ 6.0 6.1 6.2 "What is a Site-to-Site VPN?" Fortinet, www.fortinet.com/resources/cyberglossary/what-is-site-to-site-vpn. Accessed 8 Apr. 2021.
- ↑ “Different Types of VPNs and When to Use Them.” VPNMentor, www.vpnmentor.com/blog/different-types-of-vpns-and-when-to-use-them/. Accessed 12 Mar 2021.
- ↑ TunnelBear. www.tunnelbear.com/. Accessed 9 Apr. 2021.
- ↑ Calvello, Mara. "VPN Protocols: Are You Using the Right One?" Learn Hub, https://learn.g2.com/vpn-protocols 28 April. 2020, Accessed 19 Apr. 2021.
- ↑ 10.0 10.1 pp_pankaj. "Types of Virtual Private Network (VPN) and its Protocols" GeeksforGeeks, https://www.geeksforgeeks.org/types-of-virtual-private-network-vpn-and-its-protocols/ 10 Apr. 2019, Accessed 19 Apr. 2021.
- ↑ Christensson, P. "PPTP definition" TechTerms, https://techterms.com/definition/pptp 2006, Accessed 19 Apr. 2021.
- ↑ Harkness, Adam. "5 Common VPN protocols explained" NetMotion, https://www.netmotionsoftware.com/blog/connectivity/vpn-protocols 15 May. 2019, Accessed 19 Apr. 2021.
- ↑ Cite error: Invalid
<ref>tag; no text was provided for refs namedrefnetomotion - ↑ “Virtual private networks.” IEEE Potentials, vol. 20, no. 1, 2001, pp. 11-15, doi:10.1109/45.913204. Accessed 12 Mar. 2021.
- ↑ “Virtual Private Network (VPN).” Information and Technology Services, University of Michigan, its.umich.edu/enterprise/wifi-networks/vpn. Accessed 12 Mar. 2021.
- ↑ 16.0 16.1 “What is a business VPN?” Cloudflare, www.cloudflare.com/learning/access-management/what-is-a-business-vpn/. Accessed 12 Mar. 2021.
- ↑ “Why Companies Are Turning To VPNs During The Coronavirus Outbreak.” OpenVPN, openvpn.net/why-companies-are-turning-to-vpns-during-the-coronavirus-outbreak. Accessed 12 Mar. 2021.
- ↑ “The ultimate guide to VPN encryption, protocols, and ciphers.” ATT, 31 July 2019, cybersecurity.att.com/blogs/security-essentials/the-ultimate-guide-to-vpn-encryption-protocols-and-ciphers. Accessed 25 Mar. 2021.
- ↑ Levin, Benjamin. “A VPN is vital when working from home, so here’s everything you need to know.” CNN, 17 Sept. 2020, www.cnn.com/2020/09/17/cnn-underscored/how-to-setup-a-vpn. Accessed 12 Mar. 2021.
- ↑ “What is a VPN.” Cloudflare, www.cloudflare.com/learning/access-management/what-is-a-vpn/. Accessed 12 Mar. 2021.
- ↑ Economy, Elizabeth C. “The great firewall of China: Xi Jinping’s internet shutdown.” The Guardian, 29 June 2018, www.theguardian.com/news/2018/jun/29/the-great-firewall-of-china-xi-jinpings-internet-shutdown. Accessed 12 Mar. 2021.
- ↑ Shanghai, Liza Linin and Josh Chin. "China’s VPN Crackdown Weighs on Foreign Companies There." The Wall Street Journal, 2017 Aug. 2, www.wsj.com/articles/chinas-vpn-crackdown-weighs-on-foreign-companies-there-1501680195. Accessed 8 Apr. 2021.
- ↑ Bukhari, Fayaz. “India cracks down on use of VPNs in Kashmir to get around social media ban.” Reuters, 19 Feb. 2020, www.reuters.com/article/us-india-kashmir-internet/india-cracks-down-on-use-of-vpns-in-kashmir-to-get-around-social-media-ban-idUSKBN20D0LT. Accessed 12 Mar. 2021.
- ↑ Hodge, Rae. “VPN use surges during the coronavirus lockdown, but so do security risks.” CNET, 23 Apr. 2020, www.cnet.com/news/vpn-use-surges-during-the-coronavirus-lockdown-but-so-do-security-risks/. Accessed 12 Mar. 2021.
- ↑ Eddy, Max. "How to Use a VPN to Watch Netflix From Other Countries." PCMag, 20 Nov. 2020, www.pcmag.com/how-to/how-to-unblock-netflix-with-a-vpn. Accessed 9 Apr. 2021.
- ↑ Greenberg, Julia. "Netflix's CEO Says VPN Users Really Aren't a Big Deal." Wired, 18 April 2020, https://www.wired.com/2016/04/netflixs-ceo-says-vpn-users-really-arent-big-deal/. Accessed 10 April 2021.
- ↑ Parker, Jacob. "How does Netflix detect and block VPN use?" TechRader, 30 June 2020, www.techradar.com/vpn/how-does-netflix-detect-and-block-vpn-use. Accessed 9 Apr. 2021.
- ↑ "UKUSA Agreement Release." National Security Agency Central Security Service, www.nsa.gov/news-features/declassified-documents/ukusa/. Accessed 1 Apr. 2021.
- ↑ Koch, Richie. "What countries are in the 5 Eyes, 9 Eyes, and 14 Eyes aggreements?" ProtonVPN, 30 August 2018, https://protonvpn.com/blog/5-eyes-global-surveillance/. Accessed 10 April 2021.
- ↑ "Five Eyes." Privacy International, privacyinternational.org/learn/five-eyes. Accessed 8 Apr. 2021.
- ↑ Taylor, Sven. "Five Eyes, Nine Eyes, 14 Eyes – Explained." Restore Privacy, 3 Sep. 2020, restoreprivacy.com/5-eyes-9-eyes-14-eyes/. Accessed 8 Apr. 2021.
- ↑ Sharma, Mayank. “This top VPN is being sued by filmmakers.” Future US, 11 Mar 2021, www.techradar.com/news/this-top-vpn-is-being-sued-by-filmmakers. Accessed 12 Mar. 2021.
- ↑ Bischoff, Paul. "What is Torrenting? Is it Safe? Is it illegal? Are you likely to be caught?" Comparitech, 8 Apr. 2021, www.comparitech.com/blog/vpn-privacy/is-torrenting-safe-illegal-will-you-be-caught/. Accessed 9 Apr. 2021.
- ↑ “Popcorn Time VPN.” LiquidVPN, www.liquidvpn.com/popcorn-time-vpn/. Accessed 25 Mar 2021.
- ↑ “This Video Is Sponsored By ███ VPN.” YouTube, uploaded by Tom Scott, 28 Oct 2019, www.youtube.com/watch?v=WVDQEoe6ZWY.
- ↑ Whittaker, Zack. “NordVPN confirms it was hacked.” TechCrunched, 21 Oct. 2019, techcrunch.com/2019/10/21/nordvpn-confirms-it-was-hacked/. Accessed 12 Mar. 2021.
- ↑ Khan, M. T., et al. "An Empirical Analysis of the Commercial VPN Ecosystem." In Proceedings of the Internet Measurement Conference 2018, Association for Computing Machinery, 31 Oct. 2018, pp. 443-56, doi.org/10.1145/3278532.3278570. Accessed 9 Apr. 2021.
- ↑ Perta, V. et al. "A Glance through the VPN Looking Glass: IPv6 Leakage and DNS Hijacking in Commercial VPN clients." Proceedings on Privacy Enhancing Technologies, vol. 2015, no. 1, 2015, pp. 77-91, doi:10.1515/popets-2015-0006. Accessed 9 Apr. 2021..
- ↑ Smith, Adam. “NordVPN Ad Banned for Exaggerating Threat of Public Wi-Fi.” PCMag, 1 May 2019, www.pcmag.com/news/nordvpn-ad-banned-for-exaggerating-threat-of-public-wi-fi. Accessed 12 Mar 2021.
- ↑ Bischoff, Paul. "'Zero logs' VPN exposes millions of logs including user passwords, claims data is anonymous." Comparitech, 21 July 2020, www.comparitech.com/blog/vpn-privacy/ufo-vpn-data-exposure/. Accessed 12 Mar 2021.