Low Orbit Ion Cannon
|
Contents
History of Use
Anonymous, Project Chanology, and Operation Payback
The most notable usage of the LOIC client was by hacktivist group Anonymous during Operation Payback in September of 2010.
The GUI
- "Manual Mode (for pussies)" - Select this mode to manually select target and settings.
- "FUCKING HIVE MIND" - Select this mode to volunteer your computer to the hive mind, and allow it to select the target URL. Note this only allows control of the local LOIC client, and not the full machine.[3]
- IRC (Internet Resource Chat) server - Location where all machines (potentially a botnet) connect to be controlled by server administrator.
- Port - A electronic gate/path which information flows into or out of.[4] Defaults to port 80.
- "Select your target"
- "Ready?"
- "IMMA CHARGIN MAH LAZER" - Begin the HTTP/UDP/TCP bombardment of the specified address.
- "Attack options"
- Allows selection of TCP/UDP message on request log (that can be used to troll), timeout value, number of threads, and other customizations.
DoS/DDoS
DoS is an acronym that stands for "Denial of Service," and is often classified as a cyber attack. When a user attempts to visit a website, www.google.com for example, they are making a request to that page for information (ask for information that is stored in Google's servers to be loaded on the user's browser). The concept behind DoSing is that malicious attackers can continually send these HTTP/UDP/TCP requests to a website, and overload the site's capability to process all of the requests. If the attacker is able to achieve a sufficient threshold of requests, the site may "shut down" and be unable to process requests made by any user. This is where the attack coins its name as once the site is down, users that attempt to access the site are denied service to that page. [7]
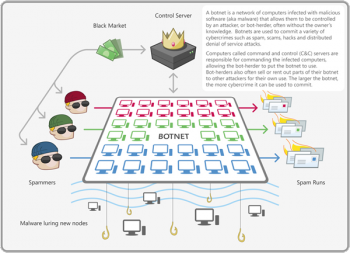
DDoS stands for "Distributed Denial of Service," and refers to a combined effort of multiple machines attempting to shut down (DoS) a site. This set of multiple machines can take the form of multiple users with individual machines, a single user with a bot-net (link/elaborate), or a combination of the two. By utilizing more than one machine, this gives the attacker(s) the ability to send more HTTP/UDP/TCP requests. The more machines, the more requests per minute, and the more likely the site will be successfully shut down. [8]
Additionally, a potential attacker may want to send more complicated queries, instead of basic call-and-response requests. If the functionality of the website is well known, there is the possibility of taking advantage of database and search mechanics. For example, rather than asking the website to ping the attacker back, the request (which is sent multiple times per minute) could be: a search that returns a million results, a complicated search that eats up computing power, or a combination of the two. [9]
Where there is power there is money: DDoS attacks can be purchased on the black market using Tor browsers. Customers can "purchase" DDoS attacks of various strengths and duration, which have an additional set of ethical implications. The attacks are fairly cheap to purchase: "$150 can buy a week-long DDoS attack on the black market," which increases the accessibility to a powerful tool by the general public.[8]
While there are many other types of DoS attacks and methods, we limit this article to the description above, as it relates most closely to LOIC.
Damage
From a user point-of-view, a service-denial attack makes the website that the user is trying to visit inaccessible. Examples of outcomes would be as subtle as the inability to read an article online, or as extremely disruptive as having a bank's login portal be unreachable. From the website owner's point-of-view, a service-denial attack can potentially be catastrophic. On the mildest end, the server would just need to be rebooted and brought back online, on the most extreme end, this attack could potentially bring down a company.
Perhaps even more detrimental than monetary losses is the exposure of a company's online weaknesses . Websites can be brought online again and systems rebooted, but once a website is shown to be insecure, a company's goods and services may also be deemed insecure. For example, on New Years Eve 2015, BBC.com, the website of one of the largest public service broadcasters in the United Kingdom, was taken down because of major DoS attack[10]. This attack targeted BBC's entire network of websites as well as their iPlayer streaming service and thousands of users were reporting having "Internal Server Errors" at 8:30AM on New Years Day. BBC later published an apology and article of the attack, but the attack did hurt the public image, as security experts noted that BBC should have been protected against such an attack because of how much data is requested every day. Many Twitter users tweeted out various jokes about the website with the hashtag #bbcdown.
While perpetrators can usually get away with attacks while remaining in the shadows, the true damage of the attack comes from shining the spotlight upon the company's weaknesses. Even if only a small amount of data is leaked after a LOIC attack (granted that the attack yields some publishable material), the loss in customer trust in the future can potentially be far more economically crippling than the cost of a server reboot.[11]
- Loss of intellectual property
- Infection of viruses
Defenses Against DoSing/DDoSing:
One of the first lines of defense when protecting against a DoS or a DDoS attack is filtering the traffic that is coming through the network. This can take the form of having either the ISP (internet service provider) buffering the users attempting to connect or firewalls that sit on the edge of the network that attempt to identify suspicious users. By attempting to identify users that have previous association with BotNets or spamming, websites can preemptively prevent attacks. This can either take the form of rejecting requests outright, or simplify flagging them for investigation by an administrator.[13]
Another takes advantage of the optional message that is attached to any HTTP request. By default, LOIC inputs “Somos legión!” (“We are legion!”) in this message box. Therefore, one way to defend against floods that attempt to DDoS is by scrubbing requests and searching for well known strings. Scrubbing for “Somos legión!” hopefully removes many first time users that didn't change the default message, and likely don't understand the consequences of their actions. Other popular strings are “U dun goofed” and similar messages, which were popular during the Wikileaks attacks of 2010. The difficulty of this type of security comes both the inability to predict all strings that attackers could use, and the double edged sword of accidentally refusing connection to legitimate users that unfortunately have a matching blacklisted string in their URL.[14]
A last resort to resisting being taken offline, websites can bolster their defenses through the purchase of adequate bandwidth. Because LOIC - used as a method for DoSing/DDoSing - relies mainly on congesting HTTP traffic, possessing enough bandwidth can foil most attacks made using the client. Unless the LOIC attack utilizes thousands or tens-of-thousands of machines, companies with enough money and important websites to protect can purchase enough bandwidth to resist an average LOIC attack while still hosting usual traffic. The downside to this is cost, and usually only larger companies will have the capital to use this as a last resort.[13]
- ip filtering
- tollgate
HOIC
The High Orbit Ion Cannon (HOIC) is the "big brother" of LOIC. While the low orbit cannon focuses mainly on TCP/UDP attacks, HOIC is the HTTP focused cannon.[15]
Ethical Implications
Pros
- Stress testing websites' abilities to handle large numbers of requests at a time
Another reason to allow LOIC to prevail on the internet simply falls back upon the First Amendment. The law promising freedom of religion, press, assembly, speech, and petetion of the government can be extrapolated to include the usage of LOIC. At its core, the Cannon is simply making requests to a webpage, just like any other user during that day. Opponents, however, argue that this is splitting hairs; the program may be built upon the legal accessing of a website, but attackers can't deny (especially if a site is brought down) that they used the tool for malicious activities. Clearly the hardpoint lies at the intersection of freedoms guarenteed by the First Amendment and the expectation of the website's owner that their website not be targeted and attacked.[16]
- Uniting tech community/hackers
Cons
- DDoSing a given website and "taking it down"
The true power of LOIC is realized when a large enough quantity of computers are used simultaneously. Therefore, there is an incentive to utilize botnets and use the control of many machines to implement the attack. This puts great value (and power) in the marketing of botnets, which are mainly sold or rented on the Black Market. In the scope of this article, there are two types of botnets: voluntary and involuntary (infected). As described above, LOIC's Hive Mind feature allows users to 'voluntarily' donate part of their machine to joining the botnet. However, there are also plenty of botnets that utilize machines - unbeknownst to their civilian users. Using injected malware, "botmasters" or "botherders" are able to control infected machines, usually through IRC servers. Once a couple machines are under control, it is even easier to use them to spam other computers, inject the same malware, and gain an even larger botnet. Therefore, the accumulation of larger and larger botnets are heavily incentivized as the ownership of them is very closely correlated to raw power.[17]
- anyone can use: don't understand gravity of actions
- furthering personal agendas/hurting competition/payback (all refer to purchasing of DDoS attacks)
Terms
- GUI - Graphical User Interface
- Hive Mind - The collective group of users/machines connected to LOIC IRC server
- Troll - Maliciously tease someone in order to achieve an aggressive response (that the "troll" deems to be comedic)
References
- ↑ 1.0 1.1 http://resources.infosecinstitute.com/loic-dos-attacking-tool/#gref
- ↑ https://sourceforge.net/projects/loic/
- ↑ https://en.wikipedia.org/wiki/Internet_Relay_Chat
- ↑ http://whatismyipaddress.com/port
- ↑ https://docs.oracle.com/javase/tutorial/networking/urls/definition.html
- ↑ https://en.wikipedia.org/wiki/IP_address
- ↑ https://www.us-cert.gov/ncas/tips/ST04-015
- ↑ 8.0 8.1 http://www.digitalattackmap.com/understanding-ddos/
- ↑ https://www.pluralsight.com/blog/it-ops/ethical-hacking-how-to-create-a-dos-attack
- ↑ http://www.telegraph.co.uk/news/bbc/12075679/BBC-website-crashes-and-Twitter-goes-into-meltdown.html
- ↑ http://www.tandfonline.com/doi/full/10.3402/egp.v6i4.22527
- ↑ https://lp.incapsula.com/rs/incapsulainc/images/eBook%20-%20DDoS%20Impact%20Survey.pdf
- ↑ 13.0 13.1 http://www.biztechmagazine.com/article/2013/02/three-elements-defense-against-denial-service-attacks
- ↑ https://devcentral.f5.com/articles/defending-against-the-low-orbit-ion-cannon-loic
- ↑ https://www.symantec.com/connect/blogs/high-orbit-vs-low-orbit-ion-cannonglimps-some-hacking-techniques
- ↑ https://books.google.com/books?id=_5GtAwAAQBAJ&pg=PA136&lpg=PA136&dq=loic+and+first+amendment&source=bl&ots=fhvlREIcND&sig=Wi5qMZf2LCQWvLaQ65dC-tLw--s&hl=en&sa=X&sqi=2&ved=0ahUKEwiVkdbxvdHSAhVH74MKHfJ9DFgQ6AEILjAD#v=onepage&q=loic%20and%20first%20amendment&f=false
- ↑ https://www.incapsula.com/ddos/ddos-attacks/botnet-ddos.html