Libraries and Ethical Information Technology
The study of libraries and ethical information technology refers to the moral relationship between library services and information technology methods and developments. The modern public library, concerned with the research, curation, and public dispensation of information, dates back to Roman times.[1][2] As libraries adapt to the emergence of modern Big Data and information evolutions, they are increasingly affected by changes in the information landscape.[3] Questions of ethics are being raised as the traditional card catalog system is eschewed in favor of more technology-driven software, such as the Integrated Library System. Additionally, Big Data and the Internet of Things (IoT) are introducing unique questions about patron privacy and information protection in libraries in addition to the ethical implications of information classification and cataloging procedures – especially so as these systems face are coming head to head with decentralized protocols.
Contents
History
Through information technology advancement, libraries have experienced diverse effects that are increasing dependencies on modern tools. Before the 1960s, much of the information handling in libraries was manual, hands-on, and self-contained; however, with the introduction of the Integrated Library System (ILS), this began to change.[4] While an ILS is an organizational construct, they commonly consist of database storage and other software features.[5] For example, a program like Sierra that allows library employees to search for a patron’s account and view all materials they currently have borrowed is a feature of the ILS.[6]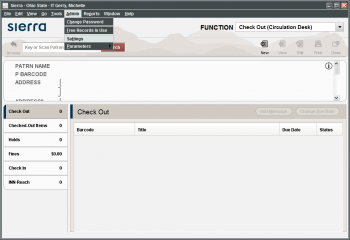
Big Data and Library Ethics
As libraries collect and dispense a wider range of data, there is more discussion about their role and responsibility concerning Big Data. Academic libraries specifically may be storing information such as full names, social security numbers, and demographics.[4] In software, completely ruling out data leaks is impossible, so inherent risks exist as libraries of any type use these systems and store sensitive information. Library professionals and ethics researchers have begun to question if it violates the aforementioned Code of Ethics to retain this sensitive information since data leaks are a lingering possibility.[4] Additionally, as libraries add resources like mobile e-book applications or special database access to help adapt to changing community needs, they are associating with Big Data companies. Prindle and Loos argue this association presents ethical challenges because Big Data is, at its core, a profit industry. For example, in 2016, it was discovered that a popular e-book company used by libraries was collecting personal information.[4] These decisions and incidents demonstrate the ethics of how patron information is no longer merely handled by librarians but also by the third-party companies they use.
University of Michigan Library Database
University of Michigan Library services offers various publications to students and faculty for their academic use and research. This service also contains a variety of databases that include scholarly articles, dissertations, and medical publications. Information about campus activities is also readily available. Additional helpful resources would be the feature of “Asking a Librarian.”[8]
(De)Censorship and Decentralization of Library Systems
As with other centrally controlled and top-down-oriented societal infrastructure, libraries have come face to face with the risks and drawbacks of remaining centrally controlled in a time of transition onto an electronic, highly networked medium. Libraries, and in fact other institutions whose primary role is to publish (i.e. televised media, newspapers, online journals), have been put in the spotlight for the past decade or two as technological advances have led to increased access, production, and need for curation. With more of the world relying on these publishing and distribution sources for information, there has been an increasing motive for these centrally controlled sources to curate and even censor information more extremely, especially as portions of the world opposed to highly liberal journalistic freedom gains unfettered access to varied sources and networks. As a result, some countries and jurisdictions have aimed to outright censor certain journalists or certain topics, constricting people's understanding of the world greatly.
Loophole Manipulation
In response, technologically oriented minds have attempted to find workarounds to censorship and centrally controlled curation of published media. One of the most popular of which is “The Uncensored Library” from the Reporters Without Borders organization. The basis of the project is to allow journalists in areas of the world that heavily censors journalistic speech to disseminate their work through a Minecraft server, which those countries actually still allow access to. Anyone with access to Minecraft can jump onto the server and read banned content.
Decentralized Technologies
Though more broadly applicable to information technology, blockchain and decentralized ledger technology have allowed for projects and protocols to create a means of publishing content independent of centrally controlled entities. The crux of these protocols is to allow the storage of information in an encrypted, decentralized manner, using a native token to cover the cost of retrieval and services built by the broader open-source community. That same open-source community is then able to build publishing and curation infrastructure on this protocol so that anyone can utilize it. One such project, Arweave, is aiming to create a “permaweb”[10] which is responsive, trustless, and totally open to various methods of storage and curation. Other projects, such as Skynet, aim to decentralize access to web applications and infrastructure[11], much of which may well be the cornerstones of fully decentralized libraries. Other forms of publication, like scientific research, are beginning to experiment with the medium of blockchain as well. At the IEEE International Conference on Blockchain and Cryptocurrency in 2019, a blockchain-based platform for scientific publishing called “Eureka” was introduced[12]. As a prototype framework for Scientific publishing on a blockchain system, the main benefit lies in alleviating the current crisis in scientific work by crypto economically incentivizing[13] review of scientific papers. Though concerns still exist for how well this will alleviate current ethical challenges to do with funding, a new layer for transparent and decentralized economic incentive in research is a welcome domain for finding new solutions.
Ethical Classification
Libraries also face challenges in ethical classification practices. The Library of Congress Classification (LCC) and the Dewey Decimal Classification (DDC) have, over time, perpetuated stereotypes or biases. The LCC and DDC are widely used classification systems across the United States and the world: thus, these system's organizations can set an important precedent. Some argue that sustaining a goal of neutrality is unrealistic and even harmful. Some claim information science should educate librarians to expect and decipher inherently non-neutral information rather than only addressing the problematic classifications themselves.[14][15] Other concerns include that classification may be inherently incorrect, as hope for universality and objective representation do not accurately represent material.[16] Many contemporary ideas of classification argue for classification methods to be applied to spatial or temporal segmentation, rather.[16] This would allow for materials to expand beyond specific labels.
Library of Congress Classification system
The library of congress, both recently and historically, has been criticized for perpetuating bias in its classification system, the Library of Congress Classification (LCC). Specifically, the Library of Congress experienced requests for reform over the term “illegal alien” as a search term in the online catalog. The original version of the Dewey Decimal Classification has been questioned over a large percentage of classification being dedicated to Christianity over other religions.[14] Historically, similar complaints have been made (e.g., cataloging Asians as “Yellow Peril”).[14]
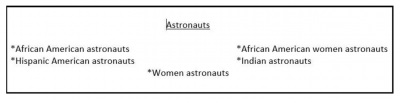
The root cause of these issues is the need to classify and sort the books within a library. The LCC system groups books based on discipline and mirrors traditional scholarly disciplines. These groups are called classes and can often branch down into subclasses for more specific information within a specific discipline.[18] As these classes are searchable, it can lead to problems with what information is returned upon a specific search query. Terms such as “Astronaut” return primarily male results and to get results about female astronauts, the term “women astronauts.” [19] The search system's structure can affect other minority groups and leads to harmful representations, as search results can impact people's perceptions about real-world diversity. [20] It has been noted library headings are in more line with information literacy guidelines and can be more effective for research. [21] Due to the many ethical issues that arise with searching library headings and the noted effectiveness, librarians that work with these materials must take special care when assisting patrons.
However, beyond just the issue of creating accurate and representative searches is the process of classification. Classifying specific books is often incredibly hard because of the wide swath of potential classes. For example, a book on basketball could be put under “sports” or “basketball” or any other potential category. While these topics may seem similar, they can be far away from each other inside the library and impact patrons who are just browsing for books. [19] Many newer classes can be created with a more ethical framework in mind, but older, more established domains are harder to change. Especially among African American studies, there often is outdated and colonial terminology and a default assumption of whiteness. [22] Thus the issue of classifying books in an accurate and meaningful manner becomes important.
Ethics of Children's Stories
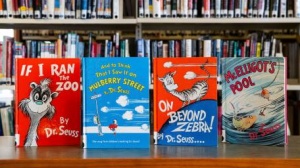
Six of Dr. Seuss's books were seized in response to images that may be perceived as racist. [24] Topics arose on how parents could broaden their child’s perspective on issues such as race and discrimination. [25] These books include: “If I Ran the Zoo,” “McElligot’s Pool,” “On Beyond Zebra!,” “Scrambled Eggs Super!,” and “The Cat’s Quizzer.” Libraries face the dilemma of whether they would like to host “controversial” books such as these in their store. Children’s literature is one of the main ways to teach values to the youth.[26] The stories and fables that are presented to children are a form of didacticism. Therefore, the morals and values presented by children’s literature are a controversial topic. Simplistic moral messaging is more successful in warning children against poor behavior and explaining the ethical implications of the stories.[26]
Weeding
Libraries use the method of “weeding” to control the quantity and quality of material brought into the establishment.[27] Weeding refers to the methods libraries employ to systematically remove resources based on specific criteria that remove their eligibility for distribution[28]. Weeding covers all types of media and is not limited to children’s books. Some considerations for weeding resources include poor content, condition, circulation, and more.[28] An example of poor content would be outdated, racist, biased, or sexist content. When a resource is damaged beyond repair, the resource would be removed on the grounds of poor condition. The practice of weeding can be considered controversial since it could be misconstrued as censorship or a threat to public access to information.[29] Some libraries do not practice weeding because of “the public’s perception of the library as safe places for materials."[30] Other libraries consider weeding a core value and practice it frequently to maintain the integrity of the information at hand.[30] Weeding is not as effective of a process for e-library management, since physical space and storage are not issues. Overall the benefits of weeding include increased accessibility of physical collections and increased customer service due to organization.[31]
Library Initiative OCLC Research
An award granted to OCLC has allowed a diverse group of individuals to come together and improve many different “practices, tools, and workflows in libraries.”[32] This initiative is part of an extensive project. Through this new initiative, OCLC plans to discuss the systemic biases and racial topics within the current library collection with stakeholders. OCLC also plans to communicate with other libraries that may benefit from gaining additional inclusive collections with their library. [33] This is made possible by working in consultation with Shift Collective. Shift Collective is a nonprofit group that aids in consultation for building stronger cultural communities.[34]
Ethical Data Practices for Academic Libraries

Given the risks associated with collecting and not collecting library data, libraries are changing their response to the increasing pressures to participate in learning analytics initiatives and the collection and analysis of usage data. Removing identifying information from stored datasets is used to mitigate or eliminate risks from unintended disclosure of this type of data.[36] However, even de-identifying a dataset by destroying the links between individually identifying information and other data is possibly insufficient to protect research subjects’ privacy.[37]
Due to the difficulty of securing “big data” and the legal and ethical risks of disclosure, it should be thought of as a “toxic asset” and treated accordingly. The best way to protect risky data is not to create it. The second best way is to destroy it as soon as possible after the analysis is complete. Data destruction plans are an integral component to securely managing privacy and minimizing risks to research subjects. All studies should include a data destruction plan or a justification of why the data should be retained and for what purpose. Any datasets containing user demographic data or other identifying information should not be retained indefinitely and should be destroyed after a reasonable period following the completion of data analysis.[38]
Libraries advocate for their universities to adopt a code of practice for data related to learning analytics. In the absence of an institutional code of practice, libraries develop their own. In this way, libraries have the opportunity to become centers of expertise and best practices for collecting and using institutional data, much as they have in other areas of scholarly communication such as copyright and research data management. Given librarianship’s ethical emphasis on ensuring users' privacy, this is a natural—and indeed vital—role for librarians to play as universities continue to develop their learning analytics programs. [39]
References
- ↑ Cartwright, Mark. "Libraries in the Ancient World." World History Encyclopedia, 23 July 2019, www.ancient.eu/article/1428/libraries-in-the-ancient-world.
- ↑ Hoq, Kazi M.G. "Information Ethics and Its Implications for Library and Information Professionals: A Contemporary Analysis."Philosophy and Progress, vol. 51, 2014, pp. 37-48, doi.org/10.3329/pp.v51i1-2.17677.
- ↑ 3.0 3.1 Kim, Bohyun. “Moving Forward with Digital Disruption: What Big Data, IoT, Synthetic Biology, AI, Blockchain, and Platform Businesses Mean to Libraries.” Library Technology Reports, vol. 56, no. 2, 2020, doi:10.5860/ltr.56n2.
- ↑ 4.0 4.1 4.2 4.3 4.4 Prindle, Sarah and Amber Loos. “Information Ethics and Academic Libraries: Data Privacy in the Era of Big Data.” Journal of Information Ethics, vol. 26, no. 2, Fall 2017, pp. 22-33.
- ↑ "The Integrated Library System (ILS) Primer." Lucidea, www.lucidea.com/special-libraries/the-integrated-library-system-ils-primer.
- ↑ "Sierra." iii, www.iii.com/products/sierra-ils.
- ↑ “Professional Ethics.” American Library Association, www.ala.org/tools/ethics.
- ↑ University of Michigan Library.https://www.lib.umich.edu/
- ↑ The Uncensored Library. (2020). [1] The Uncensored Library. Retrieved Apr 15, 2021.
- ↑ Arweave Yellow Paper. (2020). [2] Arweave permaweb. Retrieved Apr 15, 2021.
- ↑ Skynet Developer Documentation. (2020). [3] Skynet Developer Docs. Retrieved Apr 15, 2021.
- ↑ A Blockchain-based Scientific Publishing Platform. (2019). [4] A Blockchain-based Scientific Publishing Platform. Retrieved Apr 15, 2021.
- ↑ EUREKA Platform - Final report. (2019). [5] EUREKA Platform - Final report. Retrieved Apr 15, 2021.
- ↑ 14.0 14.1 14.2 Noble, Safiya Umoja. Algorithms of Oppression. E-book, New York UP, 2018.
- ↑ Drabinski, Emily. “Teaching the Radical Catalog.” Radical Cataloging: Essays at the Front, edited by K.R. Roberto, McFarland & Co., 2008, pp. 198-205
- ↑ 16.0 16.1 Mai, J. (2013). Ethics, values and morality in contemporary library classifications. KNOWLEDGE ORGANIZATION, 40(4), 242-253. doi:10.5771/0943-7444-2013-4-242
- ↑ Ros, A. (2019). Official Library of Congress subject headings involving astronauts. [Digital image]. Retrieved 2021, from https://images.theconversation.com/files/260475/original/file-20190222-195861-oabd91.JPG?ixlib=rb-1.1.0&q=45&auto=format&w=754&h=172&fit=crop&dpr=1 free to use under a creative commons license
- ↑ Library of congress classification. (2014, October). Retrieved April 13, 2021, from https://www.loc.gov/catdir/cpso/lcc.html
- ↑ 19.0 19.1 Ros, A. (2019, March 20). The bias hiding in your library. Retrieved April 13, 2021, from https://theconversation.com/the-bias-hiding-in-your-library-111951
- ↑ Kay, M., Matuszek, C., & Munson, S. A. (2015). Unequal representation and gender stereotypes in image search results for occupations. Proceedings of the 33rd Annual ACM Conference on Human Factors in Computing Systems. doi:10.1145/2702123.2702520
- ↑ Grey, A., & Hurko, C. R. (2012). SO YOU THINK YOU'RE AN EXPERT: KEYWORD SEARCHING VS. CONTROLLED SUBJECT HEADINGS. Journal of the Louisiana Chapter of the ACRL, 1(4), 15-26.
- ↑ Howard, S. A., & Knowlton, S. A. (2018). Browsing through bias: The library of Congress classification and subject headings for African American studies and LGBTQIA STUDIES. Library Trends, 67(1), 74-88. doi:10.1353/lib.2018.0026
- ↑ Young, Cathy. "Hypocrisy reigns in Dr. Seuss stir". Newsday. https://www.newsday.com/opinion/columnists/cathy-young/cathy-young-dr-seuss-cancel-culture-books-racism-1.50176800
- ↑ 2021, March 29. “Are Books You Read To Your Children Controversial?”.The Newtown Bee.https://www.newtownbee.com/03292021/are-books-you-read-to-your-children-controversial/
- ↑ 2021, March 29. “Are Books You Read To Your Children Controversial?”.The Newtown Bee.https://www.newtownbee.com/03292021/are-books-you-read-to-your-children-controversial/
- ↑ 26.0 26.1 Mills, C. (2016). Ethics and children's literature. Abingdon, Oxon: Routledge.
- ↑ 2021, March 29. “Are Books You Read To Your Children Controversial?”.The Newtown Bee.https://www.newtownbee.com/03292021/are-books-you-read-to-your-children-controversial/
- ↑ 28.0 28.1 Larson, Jeanette, and Belinda Boon. CREW: a Weeding Manual for Modern Libraries. Austin, TX: Texas State Library and Archives Commission, 2012.
- ↑ III, John N. Berry. “The Weeding War: Blatant Berry.” Library Journal, November 7, 2013. https://www.libraryjournal.com/?detailStory=the-weeding-war-blatant-berry.
- ↑ 30.0 30.1 Lehman, K. (2014). Collection development and management. Retrieved from https://journals.ala.org/index.php/lrts/article/view/5265/6401
- ↑ Harveland, J. (2017). Library Inventory Methods: Using Flexibility and ... Retrieved from https://digitalcommons.du.edu/cgi/viewcontent.cgi?article=1345&context=collaborativelibrarianship
- ↑ 2021, April 1. “OCLC grant award 'to help improve library practices'”.Research Information.https://www.researchinformation.info/news/oclc-grant-award-help-improve-library-practices
- ↑ 2021, April 1. “OCLC grant award 'to help improve library practices'”.Research Information.https://www.researchinformation.info/news/oclc-grant-award-help-improve-library-practices
- ↑ Shift collective. (n.d.). Retrieved from https://www.shiftcollective.us/
- ↑ Eroğlu, Personal data perceptions and privacy in Turkish academic libraries: An evaluation for administrations, The Journal of Academic Librarianship, Volume 46, Issue 6, 2020. Accessed: April 6, 2021.
- ↑ Tene, Omer, and Jules Polonetsky. “Big Data for All: Privacy and User Control in the Age of Analytics.” Nw. J. Tech. & Intell. Prop. 11 (2012): xxvii. Accessed April 6, 2021.
- ↑ Khalil, Mohammad, and Martin Ebner. “De-Identification in Learning Analytics.” Journal of Learning Analytics 3, no. 1 (2016): 129–138. Accessed April 6, 2021.
- ↑ Schneier, Bruce. “Data Is a Toxic Asset - Schneier on Security.” Accessed April 6, 2021. https://www.schneier.com/blog/archives/2016/03/data_is_a_toxic.html.
- ↑ Emmons, Mark, and Frances C. Wilkinson. “The Academic Library Impact on Student Persistence.” College & Research Libraries 72, no. 2 (2011): 128–149. Accessed: April 6,2021.
